Regulatory frameworks have shifted from permission-based models to accountability-driven ones. New global regulations require organizations to demonstrate that they have implemented concrete technical controls to reduce privacy risks. This marks a significant shift: compliance is now embedded within operational infrastructure, not confined to governance documents.
With 94% of consumers expecting strong data protection and breaches averaging $4.45 million each, organizations must learn to use data without ever putting privacy at risk. In the context of data protection in marketing, this need becomes even more urgent, as personalization must now coexist with privacy guarantees.
According to Future Marketing Insights, the EU continues to lead in PET adoption, spurred by GDPR enforcement, data-sovereignty mandates, and privacy-infrastructure investments. This evolution is encouraging many organizations to explore GDPR-proof automation as a strategic foundation for compliance and trust.
Consequently, in today’s guide, we explore how to integrate privacy-enhancing technologies into your marketing platform in alignment with GDPR requirements to build future-proof marketing analytics that can withstand regulatory and platform shifts. Let’s begin!
Why should marketers embrace PETs
Marketers should adopt PETs because they enable effective personalization while meeting rising privacy expectations and stricter global regulations. This is where privacy-enhancing technologies (PETs) in marketing plays a critical role by allowing organizations to personalize experiences ethically and securely:
- With laws like GDPR and CCPA tightening, PETs provide the technical foundation for principles such as data minimization, security, and consent.
- In a trust-driven digital environment, PETs help demonstrate a clear commitment to privacy, strengthening customer relationships.
- PETs support data analysis and collaboration without exposing individual-level information, enabling high-value marketing in a privacy-by-design model.
- As third-party cookies disappear and big platforms like Apple and Google impose stricter tracking limits, traditional cross-site tracking is becoming obsolete.
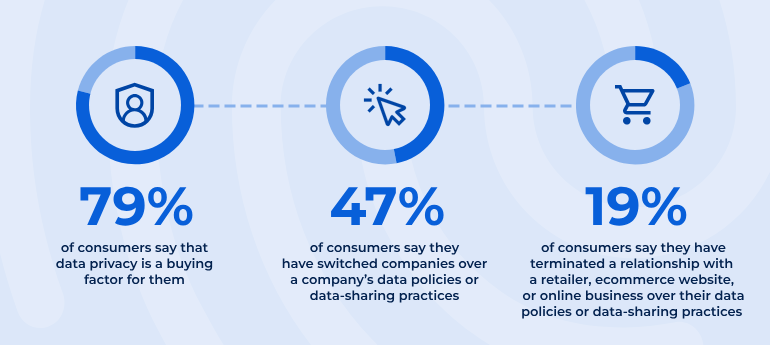
Source: Usercentrics
Adopting PETs now equips organizations for a privacy-first internet and keeps your marketing strategies resilient amid ongoing platform and regulatory changes.
Selecting the right privacy-enhancing technology
We shall be drawing on the paper “A Framework for Supporting PET Selection Based on GDPR Principles” by Sebastian Pape et al. The paper proposes a six-step methodology.
1. Describe your use-case
Start by thoroughly documenting your scenario. Define what kind of data you’re collecting, what operations you need to perform, and what the end goal is.
2. Identify entities & trust model
Map out all parties involved in data processing and establish trust relationships. Ask yourself:
- Who will process the data? (service providers, third parties, internal systems)
- How much do data owners trust each entity?
- Should processors be considered untrusted, semi-trusted, or trusted?
Three adversary models are considered: untrusted (data owner trusts no entities), semi-trusted (honest-but-curious entities), and trusted (third-party protected data).
3. Map trust models to GDPR principles
Use the framework’s trust model mapping (shown below) to identify which GDPR principles are most relevant based on your trust relationships.
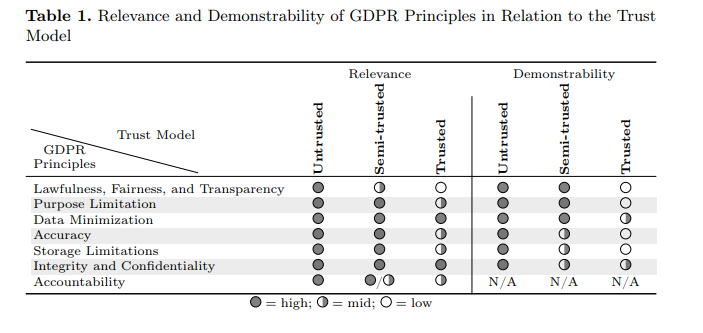
For untrusted and semi-trusted processors, principles like Purpose Limitation and Data Minimization become critical and require strong technical enforcement. For trusted processors, the assumption is they’ll comply regardless of technical measures.
4. Map GDPR principles to PET types
Once you know which GDPR principles matter most, use the framework’s mapping (as shown below) to identify candidate PET types across four layers:
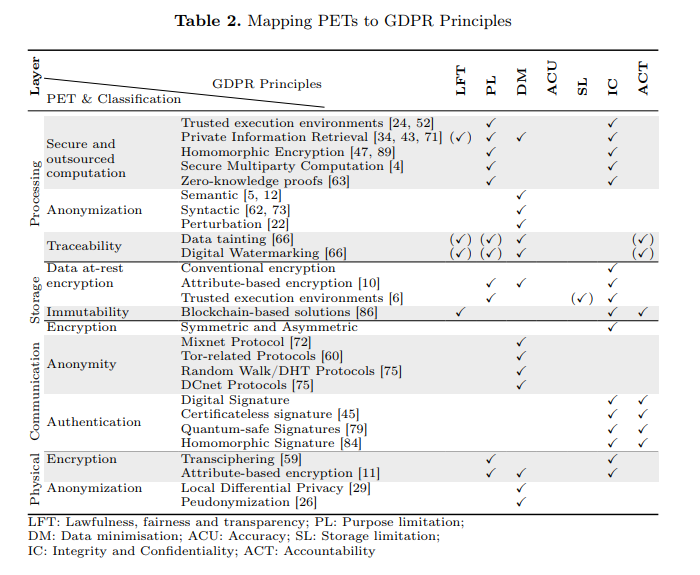
- Processing (secure computation, anonymization, traceability)
- Storage (encryption, immutability)
- Communication (encryption, anonymity, authentication)
- Physical (attribute-based encryption, pseudonymization).
This step lays the foundation for PET integration in analytics to ensure both compliance and technical feasibility.
5. Match processing needs to PET capabilities
This step involves mapping your specific computational requirements to the set of PETs that support them. Different PETs provide different privacy-preserving data processing guarantees, like deterministic encryption, order-preserving encryption, k-anonymity – each supporting different computational needs.
Determine what operations you need (e.g., addition only, multiplication, full computation) and select PETs that enable those operations while encrypted or anonymized.
6. Assess PET maturity & make trade-offs
Evaluate candidate PETs across three dimensions: Utility (does it preserve sufficient data usability?), Practicality/Scalability (can it handle your data volumes efficiently?), and Robustness (how strong are its privacy guarantees – low, medium, or high?). For example:
- Fully Homomorphic Encryption offers high robustness but has significant computational overhead.
- k-anonymity is easy to implement but provides low robustness (vulnerable to attacks).
- Differential Privacy offers medium robustness with formal guarantees but doesn’t protect individual data confidentiality.
Decision-making considerations
Before selecting a privacy-enhancing technology, it’s important to run a few foundational checks to ensure the choice fits your technical, operational, and regulatory context. This aligns with the goal of GDPR compliance for marketing analytics, which stresses both technical sufficiency and demonstrable accountability:
- Confirm your infrastructure can handle the added workload and whether real-time or batch processing is sufficient.
- Make sure the PET’s trust requirements fit your environment; for instance, whether it needs multiple independent servers or a semi-trusted partner.
- Be clear on your trade-offs: how much delay you can tolerate, how much data accuracy you can afford to lose, and whether stronger privacy protections justify heavier processing costs.
- Eliminate options that demand capabilities you don’t have; are vulnerable to threats you face; or lack mature, well-tested implementations.
- Use tools with reliable libraries, existing team expertise, and manageable long-term costs.
- Test options with real data and hardware to validate performance and communication overhead.
- Map each PET to the GDPR principles it supports, identify where additional measures are needed, and evaluate whether combining PETs adds unnecessary complexity compared to simpler organizational controls.
The core trade-off you must manage is between Data Utility (the value/accuracy you get from the data) and Privacy Protection (the strength of the guarantee that individual data is protected).
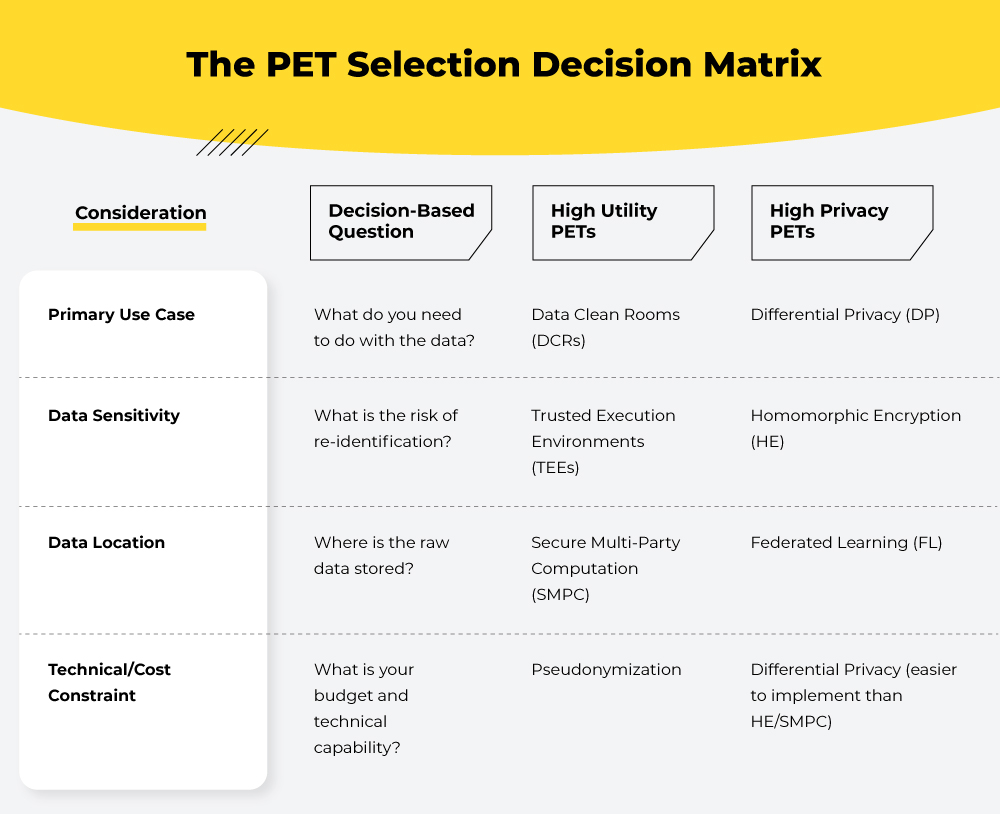
Before choosing a PET, your team should pin down three essentials: the regulatory minimum by identifying which rules (such as GDPR) apply; the required utility by defining the minimum accuracy or granularity needed for effective marketing; and the threat model by clarifying who you’re protecting the data from so the PET’s security guarantees fit the risk.
Challenges in, & solutions for, adopting PETs
1. Status quo resistance
Organizations are anchored to long-standing processes, making change feel risky. The “we’ve always done it this way” mindset slows adoption of PETs. Highlighting the impact on data protection in marketing can help leaders see PETs as a core business enabler rather than a compliance checkbox.
The path forward is to recast PETs as a business imperative.
Show how competitors win with stronger privacy, link adoption to contract requirements, highlight the catastrophic cost of breaches, and position PETs as risk-mitigation investments.
2. Multidisciplinary skills gap
Modern PETs demand technical depth—data science, cryptography, advanced statistics—that traditional privacy teams often lack, especially in smaller organizations.
The solution is multidisciplinary execution: blend privacy and technical expertise, use automation-heavy PETs like synthetic data, partner with mature organizations, rely on built-in cloud privacy tools, and bring in external experts when needed.
3. Regulatory uncertainty
Organizations struggle with unclear standards for what counts as “de-identified enough,” unrealistic “zero-risk” expectations from legal teams, and inconsistent rules across jurisdictions. This leads to paralysis.
Progress requires clearer regulatory guidance, defined acceptable risk thresholds, cross-jurisdiction consistency, sandboxes for experimentation, codes of practice, and public recognition of organizations doing it right.
4. Communication complexity
PETs are hard to explain, even among experts. Poor communication can erode trust, especially in a skeptical public environment. This is where privacy-enhancing technologies (PETs) in marketing must evolve—not just to implement PETs, but to communicate their value effectively.
Organizations need robust communication plans: layered explanations, outcome-focused messaging, real examples, public education, proactive transparency, and sometimes pausing implementation until communication is ready.
5. Scale & complexity
PIAs are no longer enough. PETs introduce multiple risk layers—individual, group, societal, compliance, reputational—each with different stakeholders and tradeoffs. Firms adopting GDPR-proof automation must consider scalability, accountability, and governance as integrated responsibilities.
Organizations must adopt broader frameworks such as Data Impact Assessments, ethics boards, benefit analyses, human-in-the-loop oversight, and context-specific reviews.
6. Small-organization resource constraints
Smaller entities face limited budgets, skills, and bandwidth, yet the consequences of a breach are disproportionately severe. Practical steps include focusing on data transformations first, investing in education, using privacy features already available in existing platforms, building process discipline, and partnering with sector anchor organizations. Finally, regulators can help through checklists, proportionate frameworks, and accessible learning modules.
7. Lack of standardization
Every organization evaluates PETs differently, slowing collaborative models and forcing repeated negotiations. However, without common standards, alignment can take years.
The fix is sector-wide consistency: shared risk frameworks, pre-approved methodologies, codes of practice, unified data-platform standards, and collective norm-setting across institutions.
Getting started with data protection in marketing
Privacy-Enhancing Technologies aren’t add-ons to modern analytics—they’re the foundation. GDPR compliance for marketing analytics is not about documentation; it’s about engineering accountability into the data infrastructure. Early adopters aren’t overengineering compliance; they’re building the infrastructure that regulators will require, partners will expect, and consumers will reward.
As organizations push toward future-proof marketing analytics, they must prioritize scalable architectures, collaboration, and robust PET integration in analytics to unlock long-term advantage—rather than scrambling to retrofit compliance under pressure.
Looking to assess your current analytics stack, select the right PETs, or build a privacy-by-design roadmap? Schedule a no-obligation call with our lifecycle marketing experts today!